Most of the web vulnerabilities in 2013 were based on browser plugin vulnerabilities. Among those, Adobe Flash, Adobe Acrobat Reader and Java Web Plugin.
The critical vulnerabilities allow code to be run outside the plugin sandbox giving all kind of possibilities to malwares coders!
The problem with these vulnerabilities is that most users are not using the most recent versions of the plugins, leaving them vulnerable to old, well documented exploits. As an example, the statistics of Java plugin version ran by users on the web: http://bit.ly/javaage
To Google Chrome’s credit, Chrome is doing a good job automatically updating its embedded version of Flash and telling you when you’re running an outdated version of Java plugin.
A simple protection is to prevent plugin execution. Chrome offers a “Click to play” for plug-ins which makes it a viable option for daily browsing.
Enable Click to Play for the plugins
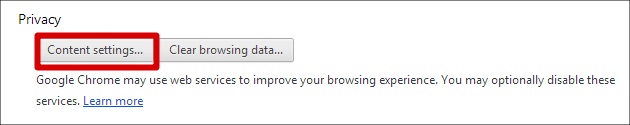
In the Google Chrome settings, Got to “Content settings” under Privacy:
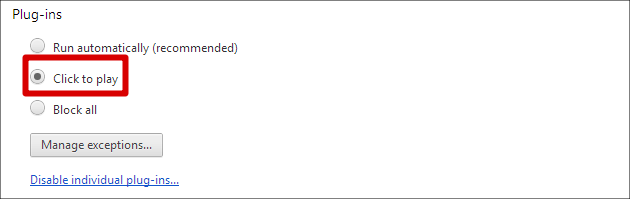
Enable “Click to play” under Plug-ins:
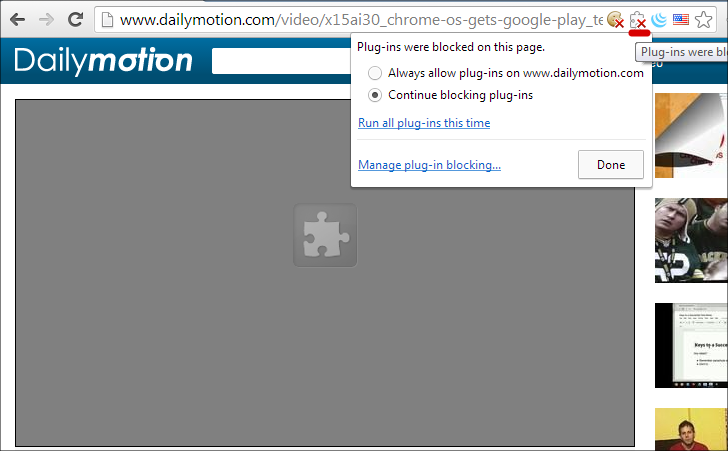
When a plugin is blocked, the “Blocked plug-ins” icon appears, clicking on it gives the option to white-list the current website.
Side effects:
- Reduces the number of advertisements displayed 🙂
- Makes it a little difficult to use certain websites such as music playback websites 🙁
Pingback: IT Administrator guide to Windows XP end of life » Martin DENIZET